Active-active without a master
Every cluster node is an equal peer — no failover, no promote, no quorum. Configuration and state are encrypted and synchronised across all nodes. Scales horizontally without limit.
Self-hosted. Open-source stack. GDPR by architecture. NetCell MailGuard places itself in front of your existing mail server via MX record — spam, phishing and malware are filtered locally on your servers. No cloud, no US third parties, no data export.
curl -fsSL https://get.netcell-mailguard.de | sudo bash
Debian 12/13 · amd64 + arm64 · Single-node or cluster
Cloud dependencies — everything on your servers
Cluster nodes — no quorum, no master/replica
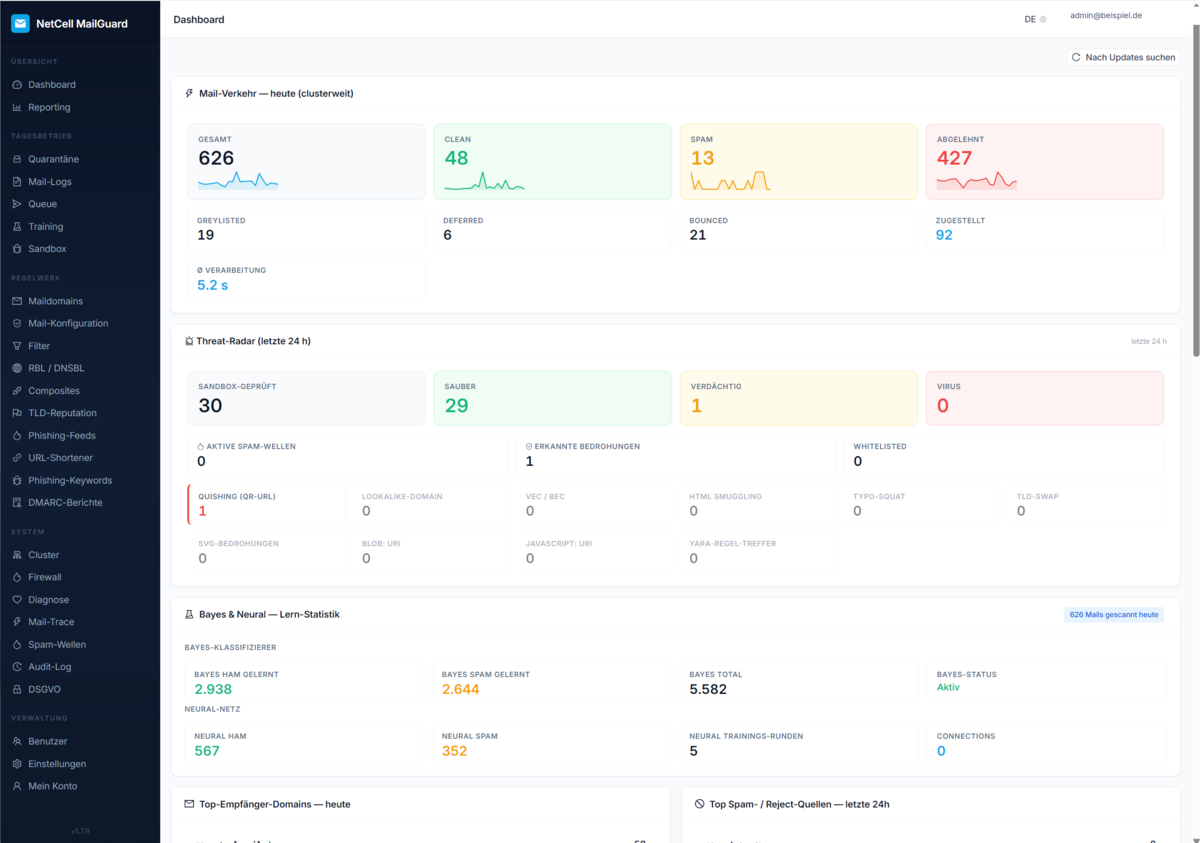
Detection layers — from DNSBL to attachment sandbox
by architecture — made in Germany, no data export
Cloud providers like Mimecast, Proofpoint and Hornetsecurity route every email through third-party infrastructure. For law firms, tax advisors, hospitals, public authorities and anyone under strict GDPR/BDSG supervision, that means a compliance nightmare with data-processing agreements, third-country transfers and standard contractual clauses. NetCell MailGuard runs on your server, in your data centre — the mail never leaves your infrastructure.
Every vendor offers SPF/DKIM/DMARC. These eight points are our real differentiators.
Every cluster node is an equal peer — no failover, no promote, no quorum. Configuration and state are encrypted and synchronised across all nodes. Scales horizontally without limit.
Self-hosted, no data export, no cloud provider between sender and recipient. No DPA, no third-country clauses. Law firms, tax advisors, public authorities and hospitals are the target audience.
Suspicious Office, PDF and archive attachments are detonated in an isolated sandbox on your server — not shipped to a cloud sandbox vendor. Operator-managed detection rules.
Patterns for German-speaking phishing waves: account-locked, tax refund, GEZ, Klarna, DHL parcel, Apple ID. English-trained cloud models often miss these.
Recipients receive a daily digest with single-click release. No admin involvement for false positives, no „can you release this mail" tickets. Token-based, secure.
Your logo, your product name, your digest subjects as a global cluster identity. Resellers sell MailGuard under their own brand — end customers don't see „NetCell MailGuard".
Every UI function is also available via REST API. API keys with scope and rate limit, OpenAPI spec as a versioned contract, webhook hooks for quarantine and reputation events.
Quarantine threshold, detection policy, DKIM keys, DMARC reporting, mail filter lists, header rewrites — all configurable per domain. One operator team manages all domains from one UI.
No failover drama on hardware failure. No promote script. No split-brain prevention. Every node processes incoming mail, every node replicates configuration changes to all others, every node can join or leave at any time.
┌──────────────┐ encrypted ┌──────────────┐
│ MailGuard │ ◀──────────────▶│ MailGuard │
│ Node 1 │ sync │ Node 2 │
│ │ │ │
│ Detection │ │ Detection │
│ stack │ ◀──────────────▶│ stack │
│ + sandbox │ │ + sandbox │
└──────┬───────┘ └──────┬───────┘
│ │
└────── MX round-robin ──────────┘
│
▼
Existing mail server
(Linux MTA / Exchange / Microsoft 365 / Google Workspace)
We bill per server, not per mailbox. EUR 29/month — whether 50 or 50,000 mailboxes pass through. Cloud email security vendors (Hornetsecurity, Mimecast, Proofpoint, Microsoft Defender for O365) typically charge EUR 2-5/mailbox: at 1,000 mailboxes that's EUR 2,000-5,000/month.
Full feature set, four weeks to evaluate
Trial activates automatically in the setup wizard — no order process required.
Production license per cluster node
Special requirements like SLA, phone support or on-premise license? Get in touch — we handle these setups individually.
MailGuard runs on your own servers — Hornetsecurity, Mimecast and Proofpoint are cloud services. With MailGuard you see every header, every detection decision, and you can audit-log every action. No US third parties, no data hand-off, GDPR by architecture.
Every cluster node is an equal peer. Configuration and state are encrypted and synchronised across all nodes. No quorum, no failover, no promote. New nodes join with a single command. Scales horizontally without limit.
No. MailGuard runs on servers or VMs in your own infrastructure. Threat-intel feeds (OpenPhish, URLhaus) are pulled — the mails themselves never leave your infrastructure.
14 layers: SPF, DKIM, DMARC, ARC, RBL/URIBL, header-anomaly detection, external phishing feeds (OpenPhish, URLhaus, PhishTank), URL-shortener resolver, DACH-specific phishing keywords, suspicious-TLD self-learning, spam scanner with ML classifier (statistical + neural + reputation), virus scanner and sandbox detonation for unknown attachments — all local per node.
Yes, with two caveats: white-label branding (logo, product name, primary colour) is one global identity per cluster — i.e. one brand outward. Per-domain configurable: digest from-address, DMARC rua-address, detection policy. If you need different brands per end customer, you either run one cluster per customer or you live with one unified reseller brand. MailGuard is single-tenant — one operator team manages all domains centrally.
30-day trial with full Standard feature set, then Standard EUR 29/server/month. No freemium — on day 31 the trial license expires and mail processing pauses. Configuration is preserved for 14 days in case you decide late. Mailbox count is never a limit. Custom licenses with SLA, phone support or on-premise perpetual on request.
Install NetCell MailGuard on your own server. 30 days free, then EUR 29 per server — no credit card required for the trial.
See pricing